Connectors Overview
This article details what a connector is, how to install a connector, and which connectors are supported in the Brinqa Platform.
What is a connector?
A connector is a stand-alone Java application that connects to a data source and retrieves data. With Brinqa connectors, organizations can automate, simplify, and streamline the process of extracting data for analysis while simultaneously accomplishing critical goals of data transformation, normalization, and contextualization.
The Brinqa connector framework formalizes the ways of interconnection between systems via Application Programming Interfaces (APIs), database extracts, and structured formats like comma-separated values (CSV), JavaScript Object Notation (JSON), and Extensible Markup Language (XML). The Brinqa connector library includes connectors to hundreds of systems covering configuration management database (CMDB), asset management, vulnerability monitoring, threat intelligence, patch management, identity provider (IDP), intrusion prevention system (IPS), security ratings, ticketing, task management, and more.
Brinqa connector store
The Integrations > Connectors page, also known as the Brinqa connector store, contains the connectors that Brinqa supports:
On this page, you can search for a specific connector by typing in the search bar, or you can click the Categories menu to filter them by their purpose (Application Security, Asset Management, Vulnerability Management, etc.).
You can also filter the connectors by selecting Installed to view the connectors you have already installed or Updates to see which connectors have available updates. Brinqa recommends that you apply updates to the connectors you have installed as soon as they are made available. You can also use the Integration+ filter to display connectors that come preconfigured with mappings to Brinqa's unified data models and attributes. See Integration+ connectors for additional information.
Install a connector
Before you can use a connector in a data integration, you must install it first. To do so, follow these steps:
-
Navigate to the connector store (Integrations > Connectors).
-
Click Integration+ to display the Integration+ connectors.
-
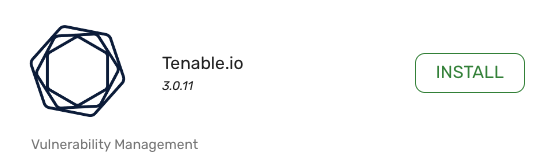
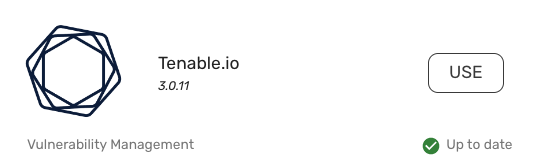
Locate the connector you want to install and click Install.
-
Once the connector is installed, the Install button turns into a Use button. Click Use to configure the connector and begin importing data.
Repeat these steps for each connector you want to use. For information on how to configure your connectors, see create a data integration and the individual connector documentation.
Update a connector
When updates for connectors become available, it's important to apply these updates to leverage the latest functionalities.
To see if a connector update is available, navigate to Integrations > Sources. The Connector version and Update available columns display the current version of the connector and whether an update is available or not, respectively.
To update an installed connector in the Brinqa Platform, follow these steps:
-
Navigate to the connector store (Integrations > Connectors).
-
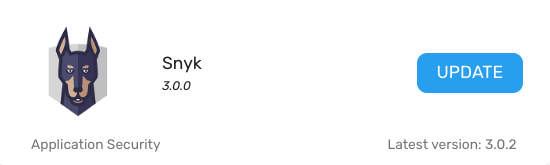
Click the Updates filter. This displays all connectors with available updates.
-
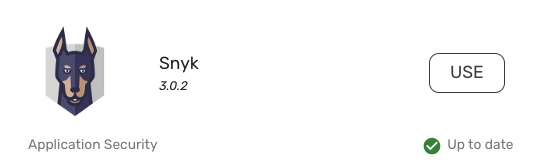
Locate the connector you want to update and click Update.
-
Once the connector has been updated, the Update button turns into a Use button.
Updating connectors can introduce a variety of new functionalities, such as support for additional objects and attributes that the connector brings in, improvements to the connector's API framework, performance improvements, bug fixes, security enhancements, and more. Brinqa recommends that you update your connectors when updates are available to ensure you are taking full advantage of the latest improvements and capabilities. For more details on the latest connector updates, see Integration+ connector releases.
Post-update steps
After updating a connector, you must update your integration to use the latest version of the connector. To do so, follow these steps:
-
Navigate to the integration page (Integration > Sources) and open your configuration.
-
Click the Connector drop-down and select the most recent version.
-
Click Next to save the changes.
-
Run the integration to verify that everything functions as expected with the updated connector.
For more information about resolving issues related to outdated connector versions, see the Troubleshooting tip.
If you need to use a previous version of a connector, please contact Brinqa Support.
How Brinqa secures your connector credentials
Brinqa implements a robust security framework to ensure that sensitive data, such as your API keys, client secrets, and passwords, are securely stored and protected from unauthorized access. Some ways that Brinqa secures your credentials includes:
-
Encryption: All credentials, such as client secrets, passwords, and API keys, are encrypted before they are stored in Brinqa's secure vault database. We use industry-standard encryption algorithms to protect data both at rest and in transit. Your credentials are never exposed in plain text.
-
Secure storage: Credentials are stored in a secure vault within the Brinqa Platform. This vault provides a high level of security, ensuring that sensitive information is isolated and protected from unauthorized access.
-
Filesystem encryption: The underlying filesystem where encrypted credentials are stored is also encrypted. This additional layer of security ensures that, even if access to the storage layer is compromised, the data remains encrypted and protected.
-
Regular audits and monitoring: Brinqa conducts regular security audits to ensure that our systems comply with the latest security standards and best practices. Continuous monitoring is also in place to detect any anomalies or potential threats. This proactive approach allows us to address issues promptly and ensure the ongoing security of your credentials.
-
Compliance: Brinqa adheres to stringent security standards and compliance requirements. Brinqa's security practices are designed to meet industry regulations, and we continually update our security measures to align with evolving compliance standards.
Integration+ connectors
Integration+ connectors in the Brinqa Platform provide you with a streamlined method of bringing in and appropriately mapping your data. Integration+ connectors are pre-configured with the necessary mappings to Brinqa's unified data models (UDM) and attributes, offering you out-of-the-box compatibility with Brinqa's standardized schema for datasets. When you use an Integration+ connector, you save time and effort as you are not required to manually map the data from the connected data source to the UDM. The connector already understands how to normalize the incoming data into the format the Brinqa Platform expects, effectively "speaking the language" of the Platform.
In addition to prebuilt mappings and auto-consolidation, Integration+ connectors also apply key normalization and transformation processes to enrich your data. These include generating additional date fields, creating status values, and risk normalization, ensuring that your data is not only mapped correctly but also fully prepared for use across Brinqa's features and analytics.
While you can install and use non-integration+ connectors, Brinqa recommends using only Integration+ connectors. Using non-Integration+ connectors can lead to consolidation and data mapping inconsistencies and potential issues with your data. If you need assistance or have questions about connectors, please contact your Brinqa Support team.
Attribute mappings
In contrast to most Integration+ connectors, non-Integration+ connectors do not automatically map the data they retrieve to UDM attributes. In these cases, you, a member of your team, or a Brinqa Support specialist must manually configure the attribute mappings. Certain Integration+ connectors, such as Azure DevOps, Brinqa Connect, CSV Connector, JSON Connector, and ServiceNow, also require manual mappings due to the dynamic nature of the data they retrieve.
To view the attribute mappings, follow these steps:
-
Navigate to Administration
> Data > Models.
-
Navigate to the data model you want to view the mappings for. For example, Host.
-
On the left-hand side of the page, click Consolidation.
-
Locate the section on the page titled "Attribute mappings" to view the mappings.
For additional information on attribute mappings, see Enrich data through attribute mappings.
List of connectors
The table below details the Integration+ connectors available in the Brinqa Platform:
| Connector Name | Connector Category | Types of Data Retrieved |
|---|---|---|
| Adaptive Shield | Identity Management | Alert, Integrated User, Integration, Security Check |
| Amazon DynamoDB | Amazon Web Services | Amazon DynamoDB Tables |
| Amazon EC2 | Amazon Web Services | Instance |
| Amazon Inspector | Amazon Web Services | AWS EC2 Instance, Cloud Resource, Code Vulnerability, Code Vulnerability Definition, Network Reachability Finding, Network Reachability Finding Definition, Package Vulnerability, Package Vulnerability Definition |
| Aqua Security (SaaS) | Container Security | Container, Container Image, Host, Vulnerability, Vulnerability Definition |
| Aqua Security (Server) | Container Security | Container, Container Image, Host, Vulnerability, Vulnerability Definition |
| AssetNote | External Attack Surface Management | Cloud Asset, IP Address, Sub Domain, Vulnerability, Vulnerability Definition |
| Axonius | Asset Management | Device |
| Black Duck Continuous Dynamic | Application Security | Application, Attack Vector, Finding, Issue, Site, Vulnerability Definition |
| Black Duck SCA | Application Security | Component, Component Version, Open Source Finding, Open Source Finding Definition, Project, Project Version |
| BitSight | Security Rating Services | Asset, Company, Finding |
| Bugcrowd | Application Security | Program, Submission |
| Burp Suite Enterprise | Application Security | Issue, Issue Definition, Scan, Site |
| Burp Suite Professional | Application Security | Dynamic Code Finding, Dynamic Code Finding Definition, Site |
| Censys | External Attack Surface Management | Certificate, Domain, Host, Risk Event, Risk Instance, Risk Type, Storage Bucket |
| Checkmarx One | Application Security | Application, Infrastructure Code As Finding, Open Source Code Finding, Open Source Code Finding Definition, Package, Project, Scan, Static Code Finding, Static Code Finding Definition |
| Checkmarx SAST | Application Security | Application, Assessment, Code Project, Open Source Finding, Open Source Finding Definition, Package, Static Code Finding, Static Code Finding Definition, Team |
| Check Point CloudGuard | Cloud Security | Alert, Alert Definition, Cloud Resource |
| CISA Known Exploited Vulnerabilities | Threat Intelligence | Exploited Vulnerability |
| Claroty xDome | Operational Technology (OT) Security | Device |
| Contrast Security | Application Security | Application, Library, Server, Vulnerability, Vulnerability Definition |
| Cortex | System Management | Catalog, Person, Team |
| CrowdStrike Cloud Security | Cloud Security | Detection, Image, Vulnerability |
| CrowdStrike Endpoint Security | Endpoint Protection | Device, Vulnerability, Vulnerability Definition |
| CSV Connector | File | Database records |
| CyCognito | Attack Surface Management | Certificate, Domain, IP Address, IP Range, Issue, Issue Definition, Web Application |
| Device42 | Asset Management | Customer, Device, Subnet |
| First EPSS | Threat Intelligence | EPSS |
| Fleet | Asset Management | Host, Installed Package, Package, Vulnerability, Vulnerability Definition |
| Flexera IT Visibility | Configuration Management | Software |
| Flexera Software Vulnerability Research | Vulnerability Management | Advisory, Product, Product Release, Vendor, Vulnerability Definition |
| Forescout eyeInspect | Operational Technology (OT) Security | Alert, Alert Definition, Asset, Vulnerability, Vulnerability Definition |
| Fortify Static Code Analyzer | Application Security | Code Project, Static Code Finding, Static Code Finding Definition |
| Fortify WebInspect | Application Security | Dynamic Code Finding, Finding, Site |
| GitLab | Application Security | Code Project, Code Repository, Open Source Finding, Open Source Finding Definition, Package, Person, Static Code Finding, Static Code Finding Definition |
| GitHub | Application Security | Code Repository, Open Source Finding, Open Source Finding Definition, Package, Secret Scanning Alert, Secret Scanning Alert Definition, Static Code Finding , Static Code Finding Definition |
| Google Cloud Asset Inventory | Google Cloud | Compute Instance |
| Google Security Command Center | Google Cloud | Bucket, Compute Instance, Finding, Finding Definition, Firewall |
| HackerOne | Application Security | Activity, Pentest Finding, Pentest Finding Definition, Site, Weakness |
| InfoBlox DDI | Network Management | Host, Network |
| Intigriti | Application Security | Pentest Finding, Pentest Finding Definition, Program, Site |
| Invicti | Application Security | Issue, Issue Definition, Scan, Website |
| Ivanti Security Controls | Patch Management | Assessed Machine, CVE, Detected Patch State, Machine, Patch, Patch Applies To, Patch Scan, Product |
| Jamf Pro | Endpoint Management | Computer, Installed Software, Mobile Device, Person, Software |
| JFrog Artifactory | Application Security | File, Project, Repository, User |
| JFrog Xray | Application Security | Vulnerability, Vulnerability Definition |
| Jira | IT Service Management | Issue |
| Jira Cloud | IT Service Management | Issue |
| JSON Connector | File | Database records |
| LDAP | Directory Services | Computer, Group, Printer, Site, Subnet, User |
| LeanIX EAM | System Management | Application, Business Capability, Data Object, Interface, IT Component, Process, Project, Provider, Subscription, Technical Stack, User, User Group |
| ManageEngine ServiceDesk Plus | IT Service Management | Request |
| Mandiant | Threat Intelligence | Vulnerability |
| Mend.io | Application Security | Application, Code Project, Open Source Finding, Open Source Finding Definition, Package, Static Code Finding, Static Code Finding Definition |
| Microsoft Azure Compute | Microsoft Azure | Virtual Machine |
| Microsoft Azure DevOps | IT Service Management | Work Items |
| Microsoft Defender for Cloud | Microsoft Azure | Alert, Alert Definition, Assessment, Assessment Metadata, Asset |
| Microsoft Defender for Endpoint | Endpoint Protection | Machine, Vulnerability, Vulnerability Definition |
| Microsoft Endpoint Configuration Management | Configuration Management | Asset, Software Install, Software Product |
| Microsoft Intune | Endpoint Management | Host, Mobile Device |
| Microsoft Security Response Center | Threat Intelligence | Product, Security Bulletin, Security Update |
| NetBox | Network Management | Cluster, Device, Prefixes, Virtual LAN, Virtual Machine |
| NIST NVD | Threat Intelligence | Product, Vulnerability, Weakness |
| Noname Security | API Security | Application, Dynamic Code Finding, Dynamic Code Finding Definition, Site |
| NowSecure Auto | Application Security | Application, Assessment, Dynamic Code Finding, Dynamic Code Finding Definition, Static Code Finding, Static Code Finding Definition, Vulnerability Audit Record |
| Okta | Identity Management | Group, Group Member, User |
| Onapsis | System, Applications, Products (SAP) Security | Asset, Vulnerability, Vulnerability Definition |
| OpsLevel | System Management | Infrastructure, Repository, Service, Team, User |
| Orca | Cloud Security | Alert, Alert Definition, Cloud Account, Container, Container Image, Database, Function, Package, Storage, User, Virtual Machine, Virtual Machine Image, Vulnerability, Vulnerability Definition, Vulnerability Package |
| PlexTrac | Application Security | Asset, Assessment, Client, Finding |
| Prisma Cloud | Cloud Security | Account Group, Cloud Account, Cloud Resource, Violation, Violation Definition |
| Prisma Cloud Compute | Container Security | Cloud Service, Code Repository, Container, Container Image, Host, Serverless, Violation, Violation Definition, Vulnerability, Vulnerability Definition |
| Qualys Container Security | Container Security | Compliance Details, Container, Control, Exception, Host, Image, Registry, Vulnerability Container, Vulnerability Image |
| Qualys Cybersecurity Asset Management | Asset Management | Asset, Installed Software, Software |
| Qualys Policy Compliance | Compliance Management | Control, Host, Violation |
| Qualys Policy Compliance Reporting Service | Compliance Management | Host, Policy, Violation, Violation Definition |
| Qualys Vulnerability Management | Vulnerability Management | Host, Vulnerability, Vulnerability Definition |
| Qualys Web Application Scanning | Application Security | Application, Finding, Vulnerability Definition |
| RAD Security | Cloud Security | Cluster, Finding, Finding Definition, Image, Plugin, Resource, Threat Vector, Threat Vector Definition |
| Rapid7 InsightAppSec | Application Security | Application, Dynamic Code Finding, Dynamic Code Finding Definition, Site |
| Rapid7 InsightCloudSec | Cloud Security | Access Key, Bucket, Cloud Account, Cloud Log Configuration, Encryption Key, User Account, Violation, Violation Definition, Virtual Machine |
| Rapid7 InsightVM | Vulnerability Management | Host, Vulnerability, Vulnerability Definition |
| Rapid7 Nexpose Data Warehouse | Vulnerability Management | Host, Vulnerability, Vulnerability Definition |
| Rapid7 Nexpose | Vulnerability Management | Asset, Vulnerability, Vulnerability Definition |
| Recorded Future | Threat Intelligence | Vulnerability Risk, Vulnerability Risk Indicator |
| Red Hat Satellite | System Management | Errata, Host, Installed Package, Package, Product, Repository, Subscription |
| runZero | Asset Management | Asset, Vulnerability, Vulnerability Definition |
| SecurityScorecard | Security Rating Service | Company, Issue, Issue Type |
| Semgrep | Application Security | Code Project, Static Code Finding, Static Code Finding Definition |
| SentinelOne | Endpoint Protection | Application, Application Install, Device |
| ServiceNow | IT Service Management | Application, Business Service, CI Relationship, Cluster, Communication Device, Computer, Group, Group Member, Location, Mass Storage Device, Network Gear, Printer, Server, Task, User, Virtual Machine Instance |
| Snyk | Application Security | Component, Ignore, Open Source Issue, Open Source Issue Definition, Project, Static Code Issue, Static Code Issue Definition, Violation, Violation Definition |
| SonarQube | Application Security | Code Project, Static Code Finding, Static Code Finding Definition |
| Sonatype Nexus IQ | Application Security | Application, Component, Policy Violation, Policy Violation Definition, Remediation, Security Issue, Security Issue Definition |
| SQL Connector | Data Store | Database Records |
| Tanium Asset | Asset Management | Asset |
| Team Dynamix | IT Service Management | Asset, Configuration Item, Group, Location, People, Ticket |
| Tenable Nessus | Vulnerability Management | Host, Scan, Vulnerability, Vulnerability Definition |
| Tenable Web Application Scanning | Application Security | Site, Vulnerability, Vulnerability Definition |
| Tenable.io | Vulnerability Management | Assessment, Host, Vulnerability, Vulnerability Definition |
| Tenable.sc | Vulnerability Management | Host, Vulnerability, Vulnerability Definition |
| Trend Micro Cloud Conformity | Cloud Security | Access Controls Role, Account, Check, Event, Group, Report, Service, User |
| Trend Micro Deep Security | Endpoint Protection | Computer, Computer Group, Computer Intrusion Prevention, Intrusion Prevention |
| Veracode | Application Security | Application, Component, Dynamic Code Finding, Dynamic Code Finding Definition, Open Source Finding, Open Source Finding Definition, Pentest Finding, Pentest Finding Definition, Site, Static Code Finding, Static Code Finding Definition |
| VulnDB | Vulnerability Management | Product, Product Version, Vendor, Vulnerability |
| watchTowr | External Attack Surface Management | Cloud Storage, Container, Domain, Finding, Finding Definition, IP, IP Range, Mobile Application, Repository, SaaS Platform, Subdomain |
| Wiz | Cloud Security | Backup Service, Bucket, CI/CD Service, Compute Instance Group, Container, Container Image, Container Registry, Container Service, DaemonSet, Database Server, Deployment, Encryption Key, File System Service, Firewall, Issue, Issue Definition, Kubernetes Cluster, Raw Access Policy, Resource Group, Serverless, Storage Account, Subscription, Virtual Machine, Virtual Machine Image, Virtual Network, Vulnerability, Vulnerability Definition, Web Service |