Semgrep
Semgrep is an application security platform that integrates static code analysis (SAST) and software composition analysis (SCA) to detect vulnerabilities across your organization's code repositories. You can bring code project, static code finding, and open source finding data from Semgrep into Brinqa to gain a unified view of your attack surface, thus strengthening your cybersecurity posture.
This document details the information you must provide for the connector to authenticate with Semgrep and how to obtain that information from Semgrep. See create a data integration for step-by-step instructions on setting up the integration.
Required connection settings
When setting up a data integration, select Semgrep from the Connector dropdown. If you cannot find the connector in the dropdown, make sure that you have installed it first. You must provide the following information to authenticate Semgrep with Brinqa:
-
API URL: The Semgrep API URL. The default URL is
https://semgrep.dev. -
Access Token: The access token associated with the Semgrep account, which must have permissions to log in to the API server and return data.
noteThe Semgrep account must be a Team or Enterprise tier account in order for the Semgrep connector to make API calls and return data.
Create a Semgrep access token
For the Semgrep connector to use the Semgrep Web API, you must provide an access token. Semgrep does not allow retrieving the access token for an existing user, therefore, you must generate a new access token instead. To do so, follow these steps:
-
Log in to the Semgrep application at https://semgrep.dev/login.
-
Navigate to Settings and click Tokens.
-
Click API tokens and then click Create new token.
-
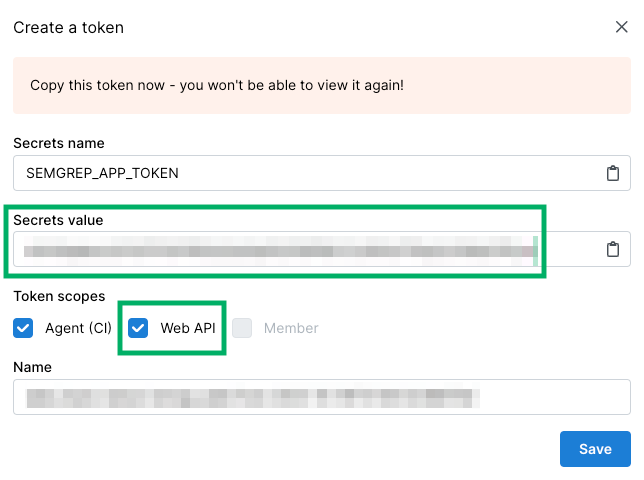
The Create a token window appears with the new token. Give the token a name or leave it as is.
You cannot view the token after this. Copy the access token (Secrets value) and save it to a secure location.
-
Under Token scopes, select Web API. This ensures that the Semgrep connector pulls information from the Semgrep Web API.
-
Click Save.
The above steps describe the minimum requirements for the Semgrep connector to work properly with Brinqa. For additional information, see Semgrep documentation.
The connector authenticates using a static API access token with a Bearer scheme. All API requests include the token in the Authorization header as Bearer <access-token>. Semgrep API tokens do not expire — they remain valid until revoked.
Additional settings
The Semgrep connector contains additional options for specific configuration:
-
Parallel requests: The maximum number of parallel API requests. The default setting is the lesser of 4 or the number of available processors.
-
Maximum retries: The maximum number of times that the integration attempts to connect to the Semgrep API before giving up and reporting a failure. The default setting is 10.
Types of data to retrieve
The Semgrep connector can retrieve the following types of data from the Semgrep API:
Table 1: Data retrieved from Semgrep
| Connector Object | Required | Maps to Data Model |
|---|---|---|
| Code Project | Yes | Code Project |
| Open Source Finding | Yes | Open Source Finding |
| Open Source Finding Definition | Yes | Open Source Finding Definition |
| Static Code Finding | Yes | Static Code Finding |
| Static Code Finding Definition | Yes | Static Code Finding Definition |
The Semgrep connector does not currently support operation options for the types of data it retrieves.
For detailed steps on how to view the data retrieved from Semgrep in the Brinqa Platform, see How to view your data.
Attribute mappings
Expand the sections below to view the mappings between the source and the Brinqa data model attributes.
Code Project
Table 2: Code Project attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| Generated (set to "Code Repository") | CATEGORIES |
| Project.default_branch | DEFAULT_BRANCH |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| Project.latest_scan_at | LAST_SCANNED |
| Project.name | NAME |
| Project.primary_branch | PRIMARY_BRANCH |
| Project.id | PROJECT_ID |
| Project.created_at | SOURCE_CREATED_DATE |
| Generated (set to "active") | STATUS |
| Project.tags | TAGS |
| Project.name | UID |
| Project.url | URL |
Open Source Finding
Table 3: Open Source Finding attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| ScaFinding.confidence | CONFIDENCE |
| ScaFinding.created_at | CREATED_AT |
| ScaFinding.location.end_column | END_COLUMN |
| ScaFinding.location.end_line | END_LINE |
| ScaFinding.external_ticket.external_slug | EXTERNAL_TICKET_SLUG |
| ScaFinding.external_ticket.id | EXTERNAL_TICKET_ID |
| ScaFinding.external_ticket.linked_issue_ids | EXTERNAL_TICKET_LINKED_IDS |
| ScaFinding.external_ticket.url | EXTERNAL_TICKET_URL |
| ScaFinding.relevant_since | FIRST_FOUND |
| ScaFinding.first_seen_scan_id | FIRST_SEEN_SCAN_ID |
| ScaFinding.found_dependency.ecosystem | FOUND_DEP_ECOSYSTEM |
| ScaFinding.found_dependency.lockfile_line_url | FOUND_DEP_LOCKFILE_LINE_URL |
| ScaFinding.found_dependency.package | FOUND_DEP_PACKAGE |
| ScaFinding.found_dependency.transitivity | FOUND_DEP_TRANSITIVITY |
| ScaFinding.found_dependency.version | FOUND_DEP_VERSION |
| ScaFinding.is_malicious | IS_MALICIOUS |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| ScaFinding.triaged_at | LAST_FIXED |
| ScaFinding.line_of_code_url | LINE_OF_CODE_URL |
| ScaFinding.match_based_id | MATCH_BASED_ID |
| ScaFinding.location | PATH |
| ScaFinding.status | PROVIDER_STATUS |
| ScaFinding.reachable_condition | REACHABLE_CONDITION |
| ScaFinding.reachability | REACHABILITY |
| ScaFinding.repository.url | REPOSITORY_URL |
| ScaFinding.review_comments[].external_discussion_id | REVIEW_COMMENT_DISCUSSION_IDS |
| ScaFinding.review_comments[].external_note_id | REVIEW_COMMENT_NOTE_IDS |
| ScaFinding.rule.message | RULE_MESSAGE |
| ScaFinding.rule_name | RULE_NAME |
| ScaFinding.ref | SOURCE_REF |
| ScaFinding.status | SOURCE_STATUS |
| ScaFinding.location.column | START_COLUMN |
| ScaFinding.location.line | START_LINE |
| ScaFinding.state | STATE |
| ScaFinding.state_updated_at | STATE_UPDATED_AT |
| ScaFinding.syntactic_id | SYNTACTIC_ID |
| ScaFinding.repository.name | TARGETS |
| ScaFinding.triage_comment | TRIAGED_COMMENT |
| ScaFinding.triaged_at | TRIAGED_AT |
| ScaFinding.triage_reason | TRIAGE_REASON |
| ScaFinding.triage_state | TRIAGE_STATE |
| ScaFinding.rule.name | TYPE |
| ScaFinding.id | UID |
| ScaFinding.usage | USAGE |
Open Source Finding Definition
Table 4: Open Source Finding Definition attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| ScaFinding.categories | CATEGORIES |
| ScaFinding.vulnerability_identifier | CVE_IDS |
| ScaFinding.vulnerability_identifier | CVE_RECORDS |
| ScaFinding.rule.cwe_names | CWE_IDS |
| ScaFinding.rule.message | DESCRIPTION |
| ScaFinding.epss_score.percentile | EPSS_PERCENTILE |
| ScaFinding.epss_score.score | EPSS_SCORE |
| ScaFinding.fix_recommendations[] | FIX_RECOMMENDATIONS |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| ScaFinding.rule.name | NAME |
| ScaFinding.rule.owasp_names | OWASP_CATEGORIES |
| ScaFinding.rule.message or ScaFinding.fix_recommendations[] | RECOMMENDATION |
| ScaFinding.rule.category | RULE_CATEGORY |
| ScaFinding.rule.confidence | RULE_CONFIDENCE |
| ScaFinding.rule.subcategories | RULE_SUBCATEGORIES |
| ScaFinding.severity | SEVERITY |
| ScaFinding.severity | SEVERITY_SCORE |
| ScaFinding.severity | SOURCE_SEVERITY |
| ScaFinding.rule.subcategories | TAGS |
| ScaFinding.rule.name | UID |
| ScaFinding.rule.vulnerability_classes | VULNERABILITY_CLASSES |
| ScaFinding.rule.cwe_names | WEAKNESSES |
Static Code Finding
Table 5: Static Code Finding attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| SastFinding.assistant.autofix.explanation | ASSISTANT_AUTOFIX_EXPLANATION |
| SastFinding.assistant.autofix.fix_code | ASSISTANT_AUTOFIX_CODE |
| SastFinding.assistant.autotriage.reason | ASSISTANT_AUTOTRIAGE_REASON |
| SastFinding.assistant.autotriage.verdict | ASSISTANT_AUTOTRIAGE_VERDICT |
| SastFinding.assistant.component.risk | ASSISTANT_COMPONENT_RISK |
| SastFinding.assistant.component.tag | ASSISTANT_COMPONENT_TAG |
| SastFinding.assistant.guidance.instructions | ASSISTANT_GUIDANCE_INSTRUCTIONS |
| SastFinding.assistant.guidance.summary | ASSISTANT_GUIDANCE_SUMMARY |
| SastFinding.assistant.rule_explanation.explanation | ASSISTANT_RULE_EXPLANATION |
| SastFinding.assistant.rule_explanation.summary | ASSISTANT_RULE_EXPLANATION_SUMMARY |
| SastFinding.click_to_fix_failures[].created_at | CLICK_TO_FIX_FAILURE_DATES |
| SastFinding.click_to_fix_failures[].reason | CLICK_TO_FIX_FAILURE_REASONS |
| SastFinding.click_to_fix_prs[].created_at | CLICK_TO_FIX_PR_DATES |
| SastFinding.click_to_fix_prs[].url | CLICK_TO_FIX_PR_URLS |
| SastFinding.confidence | CONFIDENCE |
| SastFinding.created_at | CREATED_AT |
| SastFinding.location.end_column | END_COLUMN |
| SastFinding.location.end_line | END_LINE |
| SastFinding.external_ticket.external_slug | EXTERNAL_TICKET_SLUG |
| SastFinding.external_ticket.id | EXTERNAL_TICKET_ID |
| SastFinding.external_ticket.linked_issue_ids | EXTERNAL_TICKET_LINKED_IDS |
| SastFinding.external_ticket.url | EXTERNAL_TICKET_URL |
| SastFinding.relevant_since | FIRST_FOUND |
| SastFinding.first_seen_scan_id | FIRST_SEEN_SCAN_ID |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| SastFinding.triaged_at | LAST_FIXED |
| SastFinding.line_of_code_url | LINE_OF_CODE_URL |
| SastFinding.match_based_id | MATCH_BASED_ID |
| SastFinding.location | PATH |
| SastFinding.status | PROVIDER_STATUS |
| SastFinding.repository.url | REPOSITORY_URL |
| SastFinding.review_comments[].external_discussion_id | REVIEW_COMMENT_DISCUSSION_IDS |
| SastFinding.review_comments[].external_note_id | REVIEW_COMMENT_NOTE_IDS |
| SastFinding.rule.message | RULE_MESSAGE |
| SastFinding.rule_name | RULE_NAME |
| SastFinding.ref | SOURCE_REF |
| SastFinding.status | SOURCE_STATUS |
| SastFinding.sourcing_policy | SOURCING_POLICY |
| SastFinding.location.column | START_COLUMN |
| SastFinding.location.line | START_LINE |
| SastFinding.state | STATE |
| SastFinding.state_updated_at | STATE_UPDATED_AT |
| SastFinding.syntactic_id | SYNTACTIC_ID |
| SastFinding.repository.name | TARGETS |
| SastFinding.triage_comment | TRIAGED_COMMENT |
| SastFinding.triaged_at | TRIAGED_AT |
| SastFinding.triage_reason | TRIAGE_REASON |
| SastFinding.triage_state | TRIAGE_STATE |
| SastFinding.rule.name | TYPE |
| SastFinding.id | UID |
Static Code Finding Definition
Table 6: Static Code Finding Definition attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| SastFinding.rule.category | CATEGORIES |
| SastFinding.rule.cwe_names | CWE_IDS |
| SastFinding.rule.message | DESCRIPTION |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| SastFinding.rule.name | NAME |
| SastFinding.rule.owasp_names | OWASP_CATEGORIES |
| SastFinding.rule.message | RECOMMENDATION |
| SastFinding.rule.category | RULE_CATEGORY |
| SastFinding.rule.confidence | RULE_CONFIDENCE |
| SastFinding.rule.subcategories | RULE_SUBCATEGORIES |
| SastFinding.severity | SEVERITY |
| SastFinding.severity | SEVERITY_SCORE |
| SastFinding.severity | SOURCE_SEVERITY |
| SastFinding.rule.subcategories | TAGS |
| SastFinding.rule.name | UID |
| SastFinding.rule.vulnerability_classes | VULNERABILITY_CLASSES |
| SastFinding.rule.cwe_names | WEAKNESSES |
APIs
The Semgrep connector uses the Semgrep REST API (v1). Specifically, it uses the following endpoints:
Table 7: Semgrep API Endpoints
| Connector Object | API Endpoint |
|---|---|
| Code Project | GET /api/v1/deployments/{slug}/projects |
| Open Source Finding | GET /api/v1/deployments/{slug}/findings?issue_type=sca |
| Open Source Finding Definition | GET /api/v1/deployments/{slug}/findings?issue_type=sca |
| Static Code Finding | GET /api/v1/deployments/{slug}/findings?issue_type=sast |
| Static Code Finding Definition | GET /api/v1/deployments/{slug}/findings?issue_type=sast |
Changelog
The Semgrep connector has undergone the following changes:
Table 8: Semgrep connector changelog
| Version | Description | Date Published |
|---|---|---|
| 3.0.7 | Restored spaces in object type names for Static Code Finding, Static Code Finding Definition, Open Source Finding, and Open Source Finding Definition. The spaces were inadvertently removed in v3.0.5, which caused the platform to generate differently-cased table names and created duplicate models during synchronization. Migration required: purge the duplicate tables created by v3.0.5/v3.0.6 (the lowercased variants without spaces) and perform a re-sync to repopulate the original tables. | May 12th, 2026 |
| 3.0.4 | - Moved REACHABILITY and found dependency attributes from the Open Source Finding Definition to the Open Source Finding object. - Moved assistant autotriage and component attributes from the Static Code Finding Definition to the Static Code Finding object. | February 11th, 2026 |
| 3.0.3 | Added new attributes for SAST and SCA findings in Open Source Finding, Open Source Finding Definition, Static Code Finding, and Static Code Finding Definition objects, including but not limited to FIX_RECOMMENDATIONS, REACHABLE_CONDITION, and REACHABILITY. | February 4th, 2026 |
| 3.0.2 | - The connector now retrieves the Open Source Finding and Open Source Finding Definition objects from Semgrep, adding support for ingesting SCA findings. - Updated several mappings on the Static Code Finding and Static Code Finding Definition objects. | September 26th, 2025 |
| 3.0.1 | - Fixed data type mismatches. - Code cleanup and general maintenance. | August 29th, 2025 |
| 3.0.0 | Initial Integration+ release. | January 23rd, 2023 |