CrowdStrike SaaS Security
CrowdStrike SaaS Security is a SaaS security platform that monitors and protects SaaS application environments by detecting security violations, alerts, and risks across integrated services. You can bring alert, compliance, device, host, user, and security data from CrowdStrike SaaS Security into Brinqa to construct a unified view of your attack surface and strengthen your cybersecurity posture.
This document details the information you must provide for the connector to authenticate with CrowdStrike SaaS Security and how to obtain that information from CrowdStrike. See create a data integration for step-by-step instructions on setting up the integration.
Required connection settings
When setting up a data integration, select CrowdStrike SaaS Security from the Connector dropdown. If you cannot find the connector in the dropdown, make sure that you have installed it first. You must provide the following information to authenticate CrowdStrike SaaS Security with Brinqa:
-
API URL: The CrowdStrike API URL. The default API URL is
https://<region>.crowdstrike.com.For additional information on the CrowdStrike API URL, see CrowdStrike documentation.
-
Client ID and Client secret: The client ID and client secret associated with the CrowdStrike account, which must have permissions to log in to the API server and return data.
Generate a CrowdStrike client secret
For the CrowdStrike SaaS Security connector to use the CrowdStrike API, you must provide a client secret. CrowdStrike does not allow retrieving the client secret for an existing user, therefore, you must generate a new client secret instead. To do so, follow these steps:
-
Log in to your organization's CrowdStrike Falcon portal as an administrator.
-
From the navigation menu, click Support and resources, and then click API clients and keys.
-
Click Create API client.
The Create API client window displays.
-
Fill out the Client name, Description, and select the appropriate API scopes for the user.
-
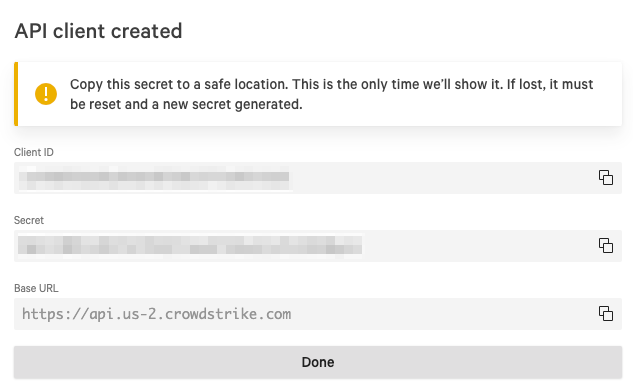
Click Create.
Your new client ID, client secret, and recommended Base URL display. You cannot view the client secret again after this. Copy and save it to a secure location.
If you do not have permissions to create a client secret, contact your CrowdStrike administrator. For additional information, see CrowdStrike documentation.
Additional settings
The CrowdStrike SaaS Security connector contains additional options for specific configuration:
-
Page size: The maximum number of records to get per API request. The default setting is 100.
-
Parallel requests: The maximum number of parallel API requests. The default setting is 1.
-
Maximum retries: The maximum number of times that the integration attempts to connect to the CrowdStrike API before giving up and reporting a failure. The default setting is 3.
Types of data to retrieve
The CrowdStrike SaaS Security connector can retrieve the following types of data from the CrowdStrike API:
Table 1: Data retrieved from CrowdStrike SaaS Security
| Connector Object | Required | Maps to Data Model |
|---|---|---|
| Alert | Yes | Alert |
| Alert Definition | Yes | Alert Definition |
| Compliance Control | No | Not mapped |
| Device | Yes | Device |
| Host | Yes | Host |
| Integrated User | Yes | Person |
| Integration | Yes | Cloud Account |
| Violation | Yes | Violation |
| Violation Definition | Yes | Violation Definition |
For detailed steps on how to view the data retrieved from CrowdStrike SaaS Security in the Brinqa Platform, see How to view your data.
Attribute mappings
Expand the sections below to view the mappings between the source and the Brinqa data model attributes.
Alert
Table 2: Alert attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| affected_diff | AFFECTED_DIFF |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| id | UID |
| integration.id | TARGETS |
| is_archived | IS_ARCHIVED |
| new_affected_count | NEW_AFFECTED_COUNT |
| Generated (set to "active") | PROVIDER_STATUS |
| security_check_api_link | SECURITY_CHECK_API_LINK |
| source | SOURCE |
| Generated (normalized "active") | SOURCE_STATUS |
| source_id | TYPE |
| timestamp | SOURCE_CREATED_DATE |
| user_who_archived | USER_WHO_ARCHIVED |
Alert Definition
Table 3: Alert Definition attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| categories | CATEGORIES |
| description | DESCRIPTION |
| id | UID |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| alert_type | NAME |
Compliance Control
Table 4: Compliance Control attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| control_title | CONTROL_TITLE |
| domain | DOMAIN |
| exposure_id | UID |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| standard | STANDARD |
Device
Table 5: Device attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| categories | CATEGORIES |
| has_user_association | HAS_USER_ASSOCIATION |
| id | UID |
| integrations | INTEGRATIONS |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| last_seen | LAST_SEEN |
| name | NAME |
| os | OS |
| os_platform | OS_PLATFORM |
| os_version | OS_VERSION |
| user_exists | USER_EXISTS |
Host
Table 6: Host attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| categories | CATEGORIES |
| has_user_association | HAS_USER_ASSOCIATION |
| id | UID |
| integrations | INTEGRATIONS |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| last_seen | LAST_SEEN |
| mac_addresses | MAC_ADDRESSES |
| name | NAME |
| os | OS |
| os_platform | OS_PLATFORM |
| os_version | OS_VERSION |
| user_exists | USER_EXISTS |
Integrated User
Table 7: Integrated User attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| categories | CATEGORIES |
| company | COMPANY |
| country | COUNTRY |
| department | DEPARTMENT |
| description | DESCRIPTION |
| domain | DOMAIN |
| emails | EMAILS |
| enabled | ENABLED |
| exposures | EXPOSURES |
| exposures_total | EXPOSURES_TOTAL |
| id | UID |
| integrations | INTEGRATIONS |
| integrations_total | INTEGRATIONS_TOTAL |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| login_names | LOGIN_NAMES |
| full_name | NAME |
| roles | ROLES |
| status | SOURCE_STATUS |
| status | STATUS |
| user_item_identity | USER_ITEM_IDENTITY |
Integration
Table 8: Integration attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| alias | ALIAS |
| categories | CATEGORIES |
| created_time | SOURCE_CREATED_DATE |
| enabled | ENABLED |
| id | UID |
| issues | ISSUES |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| last_run | LAST_SCANNED |
| name | NAME |
| saas_id | SAAS_ID |
| saas_name | SAAS_NAME |
| integration_status | SOURCE_STATUS |
| integration_status | STATUS |
Violation
Table 9: Violation attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| account_id | ACCOUNT_ID |
| account_id | TARGETS |
| affected | AFFECTED |
| base_check_id | BASE_CHECK_ID |
| base_check_id | TYPE |
| created_by | CREATED_BY |
| creation_date | FIRST_FOUND |
| creation_date | SOURCE_CREATED_DATE |
| dismiss_expiration_date | DISMISS_EXPIRATION_DATE |
| dismiss_reason | DISMISS_REASON |
| id | SECURITY_CHECK_ID |
| id | UID |
| is_global | IS_GLOBAL |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| Generated (computed from status) | PROVIDER_STATUS |
| saas_name | SAAS_NAME |
| status | SOURCE_STATUS |
| status_last_changed_date | SOURCE_LAST_MODIFIED |
| status_reason | STATUS_REASON |
| user_who_dismissed | USER_WHO_DISMISSED |
Violation Definition
Table 10: Violation Definition attribute mappings
| Source Field Name | SDM Attribute |
|---|---|
| security_domain | CATEGORIES |
| control_codes | CONTROL_CODES |
| remediation_plan | DESCRIPTION |
| id | UID |
| Generated (sync capture timestamp) | LAST_CAPTURED |
| security_check_type | NAME |
| remediation_plan | RECOMMENDATION |
| severity (normalized) | SEVERITY |
| severity (scored) | SEVERITY_SCORE |
| severity | SOURCE_SEVERITY |
Local variable indicates that the field is processed within a specific context, such as a particular workflow or calculation. Unlike other attributes, local variables aren't mapped to the unified data models. They only exist on the source data model.
Operation options
The CrowdStrike SaaS Security connector supports the following operation options. See connector operation options for information about how to apply them.
Table 11: CrowdStrike SaaS Security connector operation options
| Connector Object | Option | All Possible Values | Description | Example |
|---|---|---|---|---|
| Alert, Alert Definition | alert_type | Any valid alert type | Return only alerts or alert definitions of the specified type. | Key: alert_type Value: misconfiguration. This key and value combination only retrieves alerts of the specified type. |
| Compliance Control, Violation, Violation Definition | check_type | Any valid check type | Return only violations matching the specified check type. | Key: check_type Value: security. This key and value combination only retrieves violations of the specified check type. |
| impact | Any valid impact value | Return only violations with the specified impact level. | Key: impact Value: high. This key and value combination only retrieves violations with high impact. | |
| include_compliance | true, false | When set to true, the connector retrieves compliance control data alongside violations. Default is false. | Key: include_compliance Value: true. This key and value combination retrieves compliance control data with violation results. | |
| integration_id | Any valid integration ID | Return only violations for the specified integration. | Key: integration_id Value: abc12345. This key and value combination only retrieves violations for the specified integration. | |
| status | Any valid violation status | Return only violations with the specified status. | Key: status Value: open. This key and value combination only retrieves violations with an open status. | |
| Device, Host | integration_id | Any valid integration ID | Return only devices or hosts associated with the specified integration. | Key: integration_id Value: abc12345. This key and value combination only retrieves devices for the specified integration. |
| Integrated User | Any valid email address | Return only users matching the specified email. | Key: email Value: user@example.com. This key and value combination only retrieves the user with the specified email. | |
| integration_id | Any valid integration ID | Return only users associated with the specified integration. | Key: integration_id Value: abc12345. This key and value combination only retrieves users for the specified integration. | |
| privileged_only | true, false | When set to true, return only privileged users. | Key: privileged_only Value: true. This key and value combination only retrieves privileged users. | |
| Integration | saas_id | Any valid SaaS ID | Return only integrations matching the specified SaaS ID. | Key: saas_id Value: 12345. This key and value combination only retrieves integrations with the specified SaaS ID. |
The option keys and values are case-sensitive as they are shown in this documentation.
APIs
The CrowdStrike SaaS Security connector uses the CrowdStrike SaaS Security API. Specifically, it uses the following endpoints:
Table 12: CrowdStrike SaaS Security API Endpoints
| Connector Object | API Endpoints |
|---|---|
| Alert | GET /saas-security/entities/alerts/v3 |
| Alert Definition | GET /saas-security/entities/alerts/v3 |
| Compliance Control | GET /saas-security/entities/compliance/v3 |
| Device | GET /saas-security/entities/devices/v3 |
| Host | GET /saas-security/entities/devices/v3 |
| Integrated User | GET /saas-security/entities/users/v3 |
| Integration | GET /saas-security/entities/integrations/v3 |
| Violation | GET /saas-security/entities/checks/v3 |
| Violation Definition | GET /saas-security/entities/checks/v3 |
Changelog
The CrowdStrike SaaS Security connector has undergone the following changes:
This connector is part of a bundled release with other connectors from the same vendor. If a version shows "No change", it means that the connector version was updated for consistency as part of the bundle, but no functional changes were made to this specific connector. You can update to or skip this version without affecting your existing configuration.
Table 13: CrowdStrike SaaS Security connector changelog
| Version | Description | Date Published |
|---|---|---|
| 3.2.22 | No change. | June 9th, 2026 |
| 3.2.18 | Initial Integration+ release. | March 15th, 2026 |